|
On February 10th, 2026, the WI ICAC Task Force joined ConnectSafely in celebration of Safer Internet Day! Safer Internet Day is a global event that encourages everyone to come together and play their part in improving the internet and making it a safer place for all.
This year’s ICAC focus for Safer Internet Day was Exploitation Awareness. The WI ICAC is doing our part to #StartTheConversation and help raise awareness about growing digital threats that children face online today. This month’s Social Spotlight highlights everything you need to know about xAI/Grok.
Online Sextortion and Exploitation
In today's digital world, children are spending more time than ever online, including on social media sites and gaming platforms. As technology evolves, the threats involving exploitation and abuse continue to grow and change as well.
Three emerging, and particularly dangerous, online threats include sexually motivated sextortion, financially motivated sextortion, and sadistic online exploitation.
______________________________
Sexually Motivated Sextortion (SMS)
Sexually motivated sextortion typically involves an offender—a stranger or acquaintance, an adult or peer—obtaining sexually explicit imagery of a targeted minor—for example, by persuading or enticing the minor to create and send the imagery—and then threatening to widely distribute that imagery, or to physically harm the minor, unless the minor provides more imagery.
In many cases, these offenders are adult men who pretend to be similar age to their minor victims. The offenders’ ultimate goal in this type of sextortion scheme is to obtain sexually explicit imagery of the targeted minor. To achieve their ends, offenders often groom children and build relationships with them, sometimes over sustained periods of time.
The rise and ease-of-use of generative artificial intelligence (AI) exacerbates and complicates the threat. Now, offenders can use AI to morph a benign image of a minor (perhaps an image taken from the minor’s social media page) to create a highly realistic deepfake that appears to show the minor engaging in sexually explicit conduct. The offender then threatens to widely release that AI-generated image unless the minor produces and shares authentic sexually explicit imagery.
______________________________
Financially Motivated Sextortion (FMS)
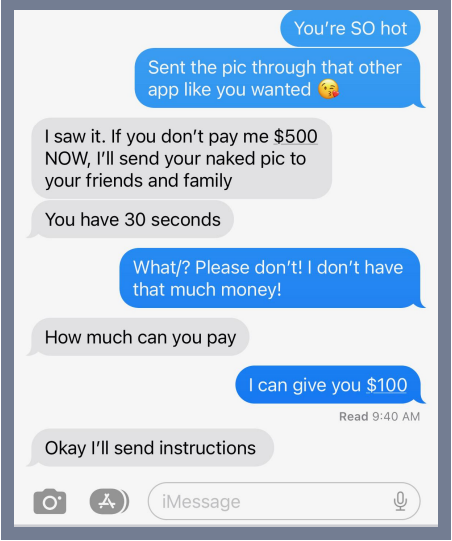
Financially motivated sextortion is similar to sexually motivated sextortion, except the offenders’ ultimate goal is money, not additional sexually explicit imagery.
With this type of sextortion, an offender may approach a child on social media after using it to learn about the child's interests, friends, school, family, etc. The offender may obtain a sexual image from the child through deceit, coercion, or some other method. In many cases, the blackmailers may have stolen or taken images of another person and they are communicating through a fake account. The blackmailer may have sent images as well.
Once the image is received, the offender quickly turns around and begins engaging in high-pressure chats, threatening to release the imagery to the minor’s friends, family, school, etc., unless the minor sends the offender money—usually in the form of payment through online payment providers or gift cards.
Here, too, generative AI exacerbates the threat. Now, offenders can (and sometimes do) take a benign image of the victim, use AI to morph that image into an image that makes it seem as though the minor is engaging in sexually explicit conduct, and then threaten to release that image unless the minor pays the offender.
The FBI and the National Center for Missing & Exploited Children (NCMEC) have reported an alarming increase in financial sextortion reports. Financial sextortion has devastating consequences for child victims, even resulting in a number of teenage boys dying by suicide as a direct result of having been the victims of this crime.
______________________________
Sadistic Online Exploitation (SOE)
Sadistic Online Exploitation presents a related but separate threat to children. With this type of victimization, offenders target vulnerable children and persuade, induce, entice, or coerce them into recording themselves engaging in various types of degrading, humiliating, and violent acts. Sometimes the offenders use threats—of violence, or to disclose sensitive material showing the victim—to coerce a victim’s compliance.
SOE offenders often operate in concert with others where they provide advice to one another, encourage one another, and share the degrading, humiliating, and violent material that they obtain from their victims—often in an effort to gain or enhance their status in the network.
______________________________
Sexually and financially motivated extortion and sadistic online exploitation are a global problem, with offenders and victims located in the U.S. and abroad, and these threats are rapidly expanding.
Check out Helping Youth Navigate Online Sextortion and Exploitation for more information about these issues, how to respond, and where to report these crimes.
|
Victimization and Warning Signs

Sextortion and online exploitation harm all sorts of children, from the particularly vulnerable (children without strong family systems, who struggle academically or emotionally, who are lonely, etc.) to those who seem to have everything going for them (strong family supports, academic / athletic / extracurricular successes, lots of friends).
With financial sextortion, teenage boys ages 13-17 are the most common targets. Offenders often target teens that appear to be popular, have good social relationships with friends and family, and have a lot to lose. Offenders engaged in sadistic online exploitation often target children and teens perceived to be more vulnerable (those that may already self-harm, have an eating disorder, depression, etc.). However, these types of exploitation can happen to any child, and child victims can be deeply traumatized as a result.
It is important to remember that children are victims—it is not their fault and they are not to blame for what has happened to them. It is imperative to remind children that no matter what, they are not alone, and it's ok to ask for help.
______________________________
|
Warning Signs

Changes in teenage behavior can be due to many different reasons. However, it is important to be aware of red flags, and remember to include online activity in regular “check-in” conversations.
Some warning signs to watch out for include:
- Self-harm
- Carving/defacing things with names or numbers
- Sudden anxiety or withdrawal
- Unexplained changes in behavior, especially after being online
- Children can be targeted in open forums or community/support groups
|
Resources and Information
There are a number of resources to learn more about the different types of sextortion and sadistic online exploitation and receive support.

Sextortion and Sadistic Online Exploitation information:
|
Reporting:
- 24-hour hotline for children and families (NCMEC):
- 1-800-THE-LOST (1-800-843-5678)
-
CyberTipline: Allows victims to file formal reports that NCMEC reviews and assesses before making available to the appropriate law enforcement agency.
|
Image Removal:
-
Take It Down: Allows children to anonymously take proactive steps in an effort to remove sexually explicit content of themselves from various online platforms.
-
StopNCII.org: While NCMEC's resources are for minors, there are others who can help adults, such as STOPNCII.org. This is a free tool designed to support victims of Non-Consensual Intimate Image (NCII) abuse.
|

Free and Confidential Support:
|

Social platforms are constantly changing and evolving and it can be challenging to stay on top of the latest trends in technology.
There are millions of apps available, therefore, it is important to focus on the various types of apps and their respective functions in order to help keep children/teens safe across all platforms.
Each month, we highlight a different app, game, or social platform and discuss how it works, possible safety risks, and ways to keep kids safe.
Here is everything parents need to know about Grok!
______________________________
|
What is Grok?
Grok is a free AI assistant who helps complete tasks, like answering questions, solving problems, and brainstorming. Grok is available to X users and is powered by xAI’s state-of-the-art large language model (LLM). Grok is designed to answer almost any question with a touch of wit and humor, while also providing helpful and insightful responses. |
|
 |
How does Grok work?

Grok utilizes next-token prediction model weights (models that predict the most likely word or symbol to follow a given text sequence) to know how to perform certain tasks. Like most LLM's today, Grok was pre-trained by xAI on a variety of data from publicly available sources and data sets reviewed and curated by AI Tutors who are human reviewers.
In responding to user queries via text or voice input, Grok has a unique feature that allows it to decide whether or not to search X public posts and conduct a real-time web search on the Internet. Grok’s access to real-time public X posts allows Grok to respond to user queries with up-to-date information and insights on a wide range of topics.
|
How old do you have to be to use Grok?

Per xAI’s Consumer Terms of Service, you must be at least 13 years old or the minimum age required in your country to use the service, and you must confirm that you meet the minimum age requirement. If you are a teenager between the ages of 13 and 17 years old, you must have your parent or legal guardian's permission to use the service, and they must agree to their Terms of Service.
Per xAI’s terms of service, while they have taken measures to limit undesirable training data and outputs, depending on the features that users choose to use, the service could produce output that is not appropriate for all ages.
|
How do you access Grok?
To use Grok, you must register for an account or log in through a third-party service such as Google, Apple, or X. By choosing to log in using a third-party service, you give xAI permission to access, use, and store your information from that service, which may include login credentials and/or access tokens for that service. If connecting using your X credentials, you may opt to bring your X user profile (including date of birth), X account and location information, and more, to your xAI account.
What are some safety considerations when using Grok?

Per the X help center, this is an early version of Grok. It may confidently provide factually incorrect information, mis-summarize, or miss some context. Users are encouraged to independently verify any information that is received and not to share personal data or any sensitive and confidential information in your conversations with Grok. This applies to any information about yourself or others.
X may also share with xAI your public X data, your user interactions, and inputs and results with Grok on X to train and fine-tune Grok and other generative AI models. It is important to keep in mind that X users have the ability to control when they want their public data to be used and can opt out of this by making your account private.
|
Moose's Corner

________________________________________________________
Moose is an Electronic Storage Detection (ESD) canine that alerts to the chemical component found in many electronic storage devices. Moose officially joined the Wisconsin ICAC Task Force in August 2023, and one of his roles will be sharing cyber safety tips in Moose's Corner each month!
_______________________________________________________
Moose's Safety Tip: Be sure to learn about emerging online harms and have ongoing conversations with children and other adults about these issues!
Stay Safe!
|
 |
|
~ Moose
|
|