|
Connecting with other people is natural when spending time online. It can be easy to meet new people, but it is not always easy to tell when someone is trying to trick or persuade you to do things. Grooming is the process where someone builds trust with a child and makes a connection to sexually exploit the child. Grooming can happen anywhere online and can occur by a stranger or by someone the child knows. Because it involves using trust against people, it can be hard to recognize when it is happening.
This month we will discuss how to identify the signs of grooming, risky app features, and tips for keeping children safe across all platforms. This month’s Social Spotlight highlights everything you need to know about the photo-sharing app, BeReal.
Harmless Apps vs. Dangerous Apps

A common question that parents want to know is which apps are the most dangerous and which ones are safe for kids. The reality is that there are potential risks on any online app or platform.
It is important to talk to children about online safety and understand the functions of different types of apps (ie. chat apps, live streaming, direct messaging, gaming, social media, etc.). There are millions of apps available -- knowing how to navigate the risks associated with different types of apps will help children stay safe across ALL platforms.
It is also important to be aware that many seemingly harmless apps may still have risky functions. Many apps have a direct messaging or chat function that allows users to send messages and photos/videos. Depending on app settings, this function may allow strangers to reach out and communicate with a child. Predators will access a child’s profile, learn about their interests, and reach out via messaging or chat to begin building a friendship or relationship with the child. They will often request to move to a different platform to continue communication or even ask for their phone number and continue via text. This can lead to grooming and eventual online enticement.
With appropriate guidance, children can use many apps and platforms safely! Privacy settings, frequent conversations about online risks, and keeping an eye on children’s online activities are essential to safe and healthy tech use.
|
Grooming

Grooming is the deliberate act of building trust with a child or teen for the purpose of exploiting them sexually. Grooming typically starts with friendship, mentorship, or kindness that gradually turns into manipulation, control, and sexual abuse or assault. Some adolescent victims report that the grooming process felt like falling in love.
Grooming is a process that occurs over weeks, months, or years and offenders will seek an isolated and often secretive relationship with a child. This process may include buying a child expensive gifts, meeting the child’s unmet emotional needs, and being actively involved in the child’s interests. The offender may treat the child as if they are older and convince them that they have a “special” relationship.
Once a relationship is established, abusers will gradually escalate their physical contact with the child to desensitize them and normalize violations of their physical boundaries. This may start with “accidental” touches before eventually initiating sexual contact.
Over 90% of child sexual abuse is perpetrated by someone the child knows and trusts. Perpetrators can be anyone: acquaintances, friends, family members, community leaders, caregivers, or adults connected to youth-serving or senior-serving organizations (schools, clubs, teams, faith-based programs, community centers, camps). Many abusers are loved and respected throughout their communities, with carefully-cultivated reputations for being helpful, compassionate, and friendly.
Teaching children and teens how to identify red flags and tricky people can help them stay safe while communicating with others online and help them identify unsafe adults in their life, whether it be someone they know or a complete stranger.
______________________________
|
Signs of Grooming

Grooming can be difficult to identify because it begins as a gradual process. Per RAINN, a key indicator of exploitation is power being misused. To identify grooming, look for patterns of behavior rather than single incidents. Red flags include:
Isolating. Persistent attempts to be alone with an intended victim; discouraging other adults’ involvement; inventing reasons for one-on-one time
Secrecy. Telling the victim to keep secrets; using private texts or DMs; asking for hidden communications; encouraging and normalizing lying
Ignoring boundaries. Excessive or unnecessary touching; disregarding privacy; making sexual jokes; facilitating “accidental” exposures to sexual content
Special treatment. Favoritism; gifts and favors without caregiver approval; compliments about the victim’s body or appearance; interest or involvement that’s unusually helpful or “too good to be true”
Role creep. Engaging the victim and family in ways that far exceed what’s expected of their role; behaving as though the relationship is closer than it actually is; repeatedly inserting themselves into the victim’s life
|
Online Enticement

Per the National Center for Missing & Exploited Children, online enticement involves an individual communicating with someone believed to be a child via the internet with the intent to commit a sexual offense or abduction.
This is a broad category of online exploitation and includes sextortion, in which a child is being groomed to take sexually explicit images and/or ultimately meet face-to-face with someone for sexual purposes, or to engage in a sexual conversation online or, in some instances, to sell/trade the child’s sexual images. This type of victimization takes place across every platform; social media, messaging apps, gaming platforms, etc.
______________________________
|
Common Tactics to Entice Children
Per the National Center for Missing & Exploited Children (NCMEC), the most common tactics used to entice children include:
- Engaging in sexual conversation/role-playing as a grooming method, rather than a goal.
- Asking the child for sexually explicit images of themselves or mutually sharing images.
- Developing a rapport through compliments, discussing shared interests or “liking” their online post, also known as grooming.
- Sending or offering sexually explicit images of themselves.
- Pretending to be younger.
- Offering an incentive such as a gift card, alcohol, drugs, lodging, transportation or food.
It is important for both parents/caregivers and children to be aware of these tactics in order to help spot possible inappropriate online interactions!
Safety Tips for Parents

Discuss the safety implications of sharing personal information online and within social media profiles; and the importance of adjusting privacy settings to limit who can see the information you share.
Know the signs of grooming and be sure children are wary of how this information may be used by offenders that wish to harm them, and teach children to watch for the warning signs that someone may not be a safe online friend.
Know that a common tactic to isolate children and continue the grooming process, or to engage in sextortion, involves asking the child to move to a different platform to continue communication and/or moving to text message.
Talk to children about healthy relationships to help them identify exploitative or unhealthy behaviors in relationships that are often part of various kinds of victimizations such as online enticement, sextortion, and child sex trafficking.
Consider regular device checks with your child and discuss why these are important. Emphasize that the intent is not an invasion of privacy, but to keep them safe and ensure that they are only communicating with people that they know and trust.
______________________________
|
Know how to report and where to access available resources!
Report child sexual exploitation to local law enforcement and to the CyberTipline.
Or contact the National Center for Missing & Exploited Children’s (NCMEC) call center at 1-800-THE-LOST (1-800-843-5678).
|
TakeItDown is a free service provided by NCMEC that can help you remove or stop the online sharing of nude, partially nude, or sexually explicit images or videos taken of you when you were under 18 years old. You can remain anonymous while using the service and you won’t have to send your images or videos to anyone.
|
Sextortion
|
NCMEC’s sextortion page offers information about what sextortion is, red flags to look out for, what to do if it happens, and additional resources.
|
|
 |
|
NCMEC's "No Escape Room" is a short, powerful, interactive film that follows a 15-year-old boy's experience with sextortion, allowing parents to see just how quickly and easily a child could fall victim to online exploitation, even while in their own home.
Learn more about new data on child sexual exploitation and the creation of this interactive experience here.
|
|
 |

Social platforms are constantly changing and evolving and it can be challenging to stay on top of the latest trends in technology.
There are millions of apps available, therefore, it is important to focus on the various types of apps and their respective functions in order to help keep children/teens safe across all platforms.
Each month, we highlight a different app, game, or social platform and discuss how it works, possible safety risks, and ways to keep kids safe.
Here is everything parents need to know about BeReal!
______________________________
|
What is BeReal?
BeReal is a photo-sharing application that allows users to post one photo per day to show their followers what they are doing in real-time. The BeReal app focuses on authenticity and asks users to be real, avoiding using filters or editing the photos. Because the app allows everyone to post only once a day, users can avoid being on the application for multiple hours throughout the day, making the app stand out from social media platforms currently dominant in the space. |
|
 |
How does BeReal work?
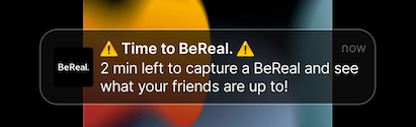
Every day, everyone in a user’s time zone receives a notification at the same time indicating it’s "Time to BeReal.” Users then have 2 minutes to open the app and take their BeReal. A BeReal isn’t just a photo. It uses the front and back cameras to capture your surroundings.
Users can retake their BeReal as many times as they want before posting. If users post outside of the two-minute window, they will be considered late and will not be able to see others’ photos until after they’ve posted. After posting, users will also gain access to the app’s Discover section.
Before posting, you can display your location or share your BeReal to the Friends of Friends feed.
If a user deletes a BeReal two times, they won’t be able to take a new one until the next BeReal notification.
|
How old do you have to be to use BeReal?

Per the BeReal terms, users must be 13 or older to create an account/use the app, but like many apps, children may find ways around this restriction and gain access.
|
Does BeReal have a direct messaging function?
Yes, BeReal now has RealChat, which allows users to chat one-on-one with people they are connected with (users cannot message anyone who hasn’t accepted their friend request). People can send as many BeReal privately to their friends as they want and even have conversations just using BeReal.
Realmoji can be used as replies to any part of a conversation including BeReal or messages. RealMojis are personalized emojis created by the user. There are six RealMojis, including an Instant RealMoji.⚡ An Instant RealMoji is a one-time live reaction to a BeReal.
What are some safety considerations when using BeReal?
Location Sharing: Sharing your location lets your friends see where you took your BeReal. By default, location sharing is turned off, but once turned on, your location will show for future BeReal posts unless turned off.
Safety Tip: You can still post and view BeReal posts with location settings turned off!
Privacy: BeReal is private by default and only visible to your friends, however, users can change the audience setting to My friends + their friends, in which your post is shared with your BeReal friends and their BeReal friends.
Inappropriate Content: Many adults use the platform, which means unfiltered photos could include sexual content, drugs/alcohol, violence, and more. Since deletion of photos is limited each day, possible inappropriate photos that were posted in a moment of poor judgment could be up for longer than intended.
Distraction: While the anticipation of not knowing when the random notification will come through may be exciting, the time-sensitive nature of the request may result in kids dropping everything to find something cool to post. This may interfere with life’s daily activities or encourage distraction, creating possible unsafe situations such as while driving or walking across the street.
Moose's Corner

________________________________________________________
Moose is an Electronic Storage Detection (ESD) canine that alerts to the chemical component found in many electronic storage devices. Moose officially joined the Wisconsin ICAC Task Force in August 2023, and one of his roles will be sharing cyber safety tips in Moose's Corner each month!
_______________________________________________________
Moose's Safety Tip: Teach children the warning signs and common tactics used to entice children, and empower them to report anything that makes them feel uncomfortable online!
Stay Safe!
|
 |
|
~ Moose
|
|